Monica is a Marketing Manager at Frontline Data Solutions. She has a background in warehouse operations and bachelor’s degrees from Indiana University in both Supply Chain Management and International Studies.
Summary
Many companies still think of management of change (MOC) as a narrow OSHA requirement that only matters when a facility falls under process safety management (PSM) rules. In practice, however, the MOC element of PSM applies to multiple regulators, not just OSHA. So, the underlying expectation is broader than any single citation. Regulators want to see that your team can identify operational changes, evaluate the risk those changes introduce, document the basis for decisions, and control implementation. That way, seemingly simple changes don’t become the starting point for an incident, shutdown, or audit finding.
That matters because change rarely arrives in a neat, controlled way. A single project can affect equipment, procedures, contractors, staffing, training, startup activities, and environmental obligations all at once. And due to poor documentation and communication, teams often can’t prove full control of their MOC process. This guide explains what regulators actually expect from an MOC program, where those expectations overlap, and how the details can shift based on industry.
Key Takeaways
- Multiple agencies have MOC requirements and all of them expect controlled, documented change management.
- OSHA and the EPA are the two regulators with formal MOC expectations in many industrial settings.
- PHMSA, BSEE, and other industry regulators reinforce the same core principle through adjacent change-control requirements.
- The biggest MOC failures usually happen in execution, not in policy design.
- A strong MOC program improves audit readiness, operational consistency, accountability, and incident prevention.
Still working on MOC compliance?
Use this guide to audit your program’s compliance with OSHA requirements before applying MOC to other ares of your business.
Why Do MOC Programs Fail Regulatory Audits?
Most companies run into MOC issues because they either don’t have a formal process or their team doesn’t follow it. In the first instance, step one to compliance is coming up with a process that you can follow and enforce. However, most cases are where there’s a documented MOC program in place and individuals or teams neglect it.
For example:
- Production teams move quickly to solve problems.
- Engineers make technical adjustments to keep a project on schedule
- Supervisors shift responsibilities to cover staffing gaps
- Contractors complete work that affects equipment or operating conditions.
Each individual decision feels reasonable in the moment, but if they don’t go through the MOC review and approval process, the MOC program becomes just a document that describes the ideal state rather than the real one.
These issues come up all the time in regulatory audits. They can look like:
- Some implemented a change before it went through approval.
- No one updated supporting procedures for a changed process, piece of equipment, etc.
- A startup happened before workers received training on it.
- Someone assumed another team was handling documentation.
- Different sites used different criteria for deciding whether something counted as a change at all.
These are signs that the company lacks a reliable process for controlling risk as conditions evolve.
Temporary Changes Affect Compliance
Temporary MOCs are also one of the easiest ways for an MOC program to fail. A team may install a bypass, change an operating parameter, use a temporary repair, alter a workflow, or rely on a contractor arrangement that was only meant to last for a short period. Over time, though, if no one’s tracking the expiration date, the temporary MOC becomes permanent. And if it doesn’t go through a formal review, it might create new risks within the facility.
That’s exactly the kind of drift that regulators view as evidence of weak process control. It creates practical operational problems. When a temporary change lingers, you’re probably relying on outdated procedures, incomplete hazard analysis, or assumptions that are no longer true. If an incident occurs, you’re left trying to explain why a short-term adjustment was still in place months later. Under scrutiny, that explanation rarely sounds strong. A defensible MOC process must treat temporary changes as active risks that need defined timelines, follow-up reviews, and formal closure.
What Do Regulators Enforce?
Regulators use different terminology, but the underlying principle is consistent: they expect you to control change before the change controls you. In a regulatory context, that means you can’t implement operational changes casually. You need to evaluate them in relation to safety, environmental impact, process integrity, documentation, training, and implementation timing. Regulators want evidence that your team understood what was changing, considered the consequences, obtained the right approvals, and communicated the change to the people affected by it.
A strong MOC process typically answers a series of practical questions:
- What exactly is changing?
- Why is are we making the change?
- What technical assumptions support it?
- What hazards or unintended consequences could result?
- Which procedures, drawings, permits, or training requirements must be updated?
- Who needs to review and approve it?
- What conditions must be met before startup or full implementation?
If you can’t answer those questions, it’ll be difficult to show that changes are under control.
This is why MOC matters well beyond compliance. It’s a bridge between engineering, operations, safety, quality, maintenance, contractors, and leadership. Without that bridge, teams may act on partial information. With it, you can show OSHA and the EPA that you’re managing changes in a disciplined way.
OSHA’s Expectations for a MOC Compliance
OSHA’s process safety management standard is the foundation of MOC. For covered processes, OSHA expects employers to establish written procedures to manage changes to any process chemicals, technology, equipment, procedures, and facilities that affect a covered process. Everyday operational changes can trigger MOC the same as major capital projects.
In practice, OSHA expects companies to
- Review the technical basis for the change
- Evaluate safety and health impacts
- Define any needed modifications to operating procedures
- Identify the period for the change when relevant
- Specify authorization requirements
The process also has to connect with communication and training. Just because some approved a change in a document doesn’t mean they’ve managed it. The people operating, maintaining, supervising, and supporting the process need to know what has changed and what that means for their work. If startup occurs before that happens, the facility already has risk exposure.
This is where many programs fail OSHA audits. A team may be good at recognizing large equipment upgrades but inconsistent with procedural changes, staffing shifts, or temporary workarounds. They might complete documentation for the initial request but not for downstream tasks like updating SOPs, drawings, alarms, or training records. Some facilities still rely on a patchwork of forms and email approvals that make it hard to see whether all required steps were actually finished. From OSHA’s perspective, those gaps matter because they show the difference between an effective process and one that just exists on paper.
The EPA’s Risk Management Plan Requirements
The EPA reinforces MOC through its Risk Management Program (RMP) rule. It requires process changes that affect safety or environmental risk to go through a formal review and implementation process. This is especially important in chemical operations, wastewater treatment, and other environments where a change can affect both worker safety and offsite consequences.
A change to equipment, chemistry, instrumentation, or procedures may influence process safety, emissions, release scenarios, emergency planning assumptions, and reporting obligations in one move. If the MOC program is fragmented, you might only address OSHA while missing the EPA requirements. That creates a false sense of security.
A stronger approach is to build an MOC workflow that addresses worker safety, environmental impact, and operational execution. That means the review process pulls in the right people, questions, and documents based on the type of change involved. If you anticipate EPA expectations instead of treating them as an afterthought, the facility is in a much better position to show that it manages change in a complete rather than compartmentalized way.
What Does PHMSA Expects from Pipeline Change Management?
The Department of Transportation’s Pipeline and Hazardous Materials Safety Administration (PHMSA) has a slightly different lens on change management. Pipeline systems raise questions about integrity, repair criteria, pressure control, inspection data, field conditions, and long-term reliability. So, changes that affect the safe operation of the system need to be evaluated, documented, and implemented under control. If pipeline operators don’t track changes that alter risk, then they don’t meet PHMSA’s requirements.
Pipeline change management often spans:
- Engineering analysis
- Maintenance execution
- Contractor work
- Records management
- Regulatory obligations
Without an MOC process, pipeline operators are much more likely to make risky decisions. For example, a technically sound field change may still create risk if you don’t update related records or trigger follow-up inspections are not triggered.
If you’re in the PHMSA space, an effective MOC program gives you a practical way to document why a change was necessary, what safety impacts were considered, who reviewed it, and what downstream actions were required. This helps to manage risk in the field while also demonstrating to regulators that change control is part of the operating system rather than a loose administrative exercise.
BSEE and MOC Under Offshore Safety and Environmental Management Systems
In high-risk offshore, process changes, mechanical changes, procedural updates, and organizational decisions can all have significant consequences. Under the Bureau of Safety and Safety Enforcement (BSSE), management of change is a formal and visible expectation. Operators expected to maintain a documented program that evaluates the safety and environmental impact of relevant changes before implementation.
Under this rule, changes to equipment, operating procedures, materials, and organizational structures need to move through a process that captures review, authorization, communication, and recordkeeping. Offshore operations are especially sensitive to breakdowns in handoff and visibility. When multiple contractors, supervisors, and technical disciplines are involved, informal coordination is not enough. Standardized change management gets the right information to the right people before a change goes live.
How CCPS Guidelines Go Beyond Regulatory Minimums
The Center for Chemical Process Safety emphasizes the importance of defining boundaries in MOC. Companies often struggle because they are inconsistent about what counts as a change. Teams might route large equipment modifications through MOC while allowing procedural changes, temporary repairs, software updates, staffing changes, or contractor-driven adjustments to happen through side channels. The CCPS pushes companies to make those boundaries explicit, so the MOC program doesn’t depend on personal judgment alone.
It also reinforces the importance of linking MOC to related processes such as pre-startup safety review, training, document control, action tracking, and incident prevention. A change is rarely complete when the approval is signed. The real measure of control is whether a team completed all action items, verified their effectiveness, and properly closed out changes. Adopting that mindset usually builds stronger programs because it stops treating MOC as a one-time form and starts managing it as an end-to-end operational process.
The Most Common MOC Gaps Across High-Risk Industries
Oftentimes, the same MOC program weaknesses show up repeatedly across facilities. The first is lack of visibility. If you use email inboxes, shared folders, spreadsheets, and local forms to track changes, you can’t easily see the status of everything. That makes it hard to prioritize work, escalate issues, or prove that you finished required steps before implementation.
The second common gap is inconsistent execution across sites or departments. Many companies have a corporate MOC process, but local sites interpret it differently. While one site may require strong documentation and cross-functional review, another might be more lenient. Over time, the company ends up with different definitions of what counts as a change, different expectations for approval, and different levels of audit readiness. That inconsistency increases risk because similar changes don’t receive similar control.
The third recurring weakness is poor follow-through. Most commonly, this means someone submits a change request or approves it but:
- The downstream work stalls
- Procedures don’t get updated
- Training is delayed
- Action items remain open
- Temporary changes are left in place with no closure date
These breakdowns create the illusion that the process is working. Regulators and auditors pay close attention to these gaps to see if the company manages change consistently or just records the start of it.
What Does a Defensible MOC Program Look Like?
A defensible MOC program is one that a regulator, auditor, plant leader, or incident investigator can follow from beginning to end without guessing what happened. It gives the company a clear and repeatable path for:
- Initiating and reviewing a change
- Documenting the technical basis
- Assigning responsibilities
- Tracking approvals
- Closing the loop when implementation is complete
This typically looks like standardized workflows, visible ownership, and centralized records. This kind of structure reduces administrative chaos while making the program easier to defend.
Just as important, a defensible program fits how industrial teams actually work. If the system is too vague, people improvise. If it’s too complicated, they work around it. The best programs create enough structure to control risk without adding so much friction that adoption collapses. That balance is where software can make a meaningful difference.
How MOC Software Takes You Beyond Compliance
Manual systems create friction at every stage of the MOC process. People have to remember who needs to review a change, send follow-up emails, dig around for supporting document, etc. In theory, a disciplined team can manage all this manually. But that discipline becomes hard to sustain as complexity, volume, and cross-functional coordination increase.
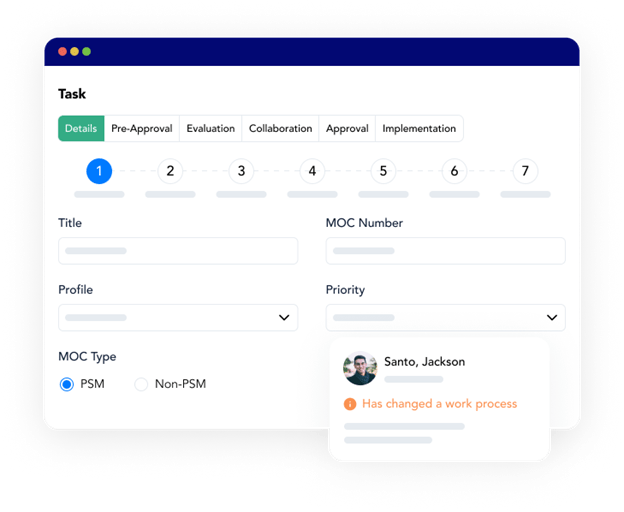
A software system like Frontline MOC simplifies all of this by:
- Guiding users through required steps
- Routing tasks to the right people
- Tracking and documenting approvals
- Centralizing MOC records
- Creating a log of all changes
It eases the administrative burden that causes teams to avoid the process in the first place. When the workflow is easy to follow and the value is obvious, adoption improves.
This matters for both compliance and performance. With higher adoption and better visibility within the MOC program, you can reduce risk, prevent incidents, and avoid rework. Software is a best practice if you want to apply the principles of MOC to areas of your business other than PSM compliance.
Customer Success Story: Improving MOC Program Performance with Frontline
The City of Las Vegas Public Works Environmental Division provides sustainable, cost-effective infrastructure services and oversees coordination with environmental laws, regulations, and permit requirements. It operates three wastewater treatment facilities, which means its teams work in an environment where operational consistency and regulatory discipline matter every day. Their team originally handled MOC activities manually which made the process difficult to sustain as activity increased.
The biggest challenge was tracking the MOC process completely by hand. Manual management created a heavy coordination challenge. People had to rely on emails, conversations, meetings, and physical files to understand where a change stood and what still needed to happen. That made it harder to maintain visibility, harder to document progress consistently, and harder to ensure that everyone was working from current information.
After recognizing those limitations, the Environmental Division invested in Frontline MOC to standardize the workflow and move change management into a central system. The software gave them a consistent path for each request, including stages such as pre-approval, new, evaluation, collaboration, approval, implementation, and startup.
With MOC activities taking place in a central hub, the team no longer had to spend the same amount of time emailing, talking through status updates, or attending meetings just to move changes forward. Documentation also improved because they could store and update records digitally. That reduced the risk of duplicate work, outdated documents, and confusion about who was responsible for what.
For the City of Las Vegas, Frontline MOC helped turn a manual, time-consuming program into a standardized workflow that saves time, improves visibility, and supports stronger regulatory compliance.
Want to take your MOC program beyond compliance? Book a demo with our sales team to learn more about the benefits of cloud-based change management.